Securing Web Widgets: Why Explicit HTTPS URLs Matter
Have you ever embedded a third-party widget or script into your index.html only to find it intermittently failing or triggering security warnings? A seemingly innocuous detail in the URL can be the culprit, especially when dealing with scheme-relative paths. On the 'patitas-al-rescate' project, we recently focused on ensuring the robust functionality of a web translation widget, which highlighted a common web development pitfall involving the proper referencing of external scripts.
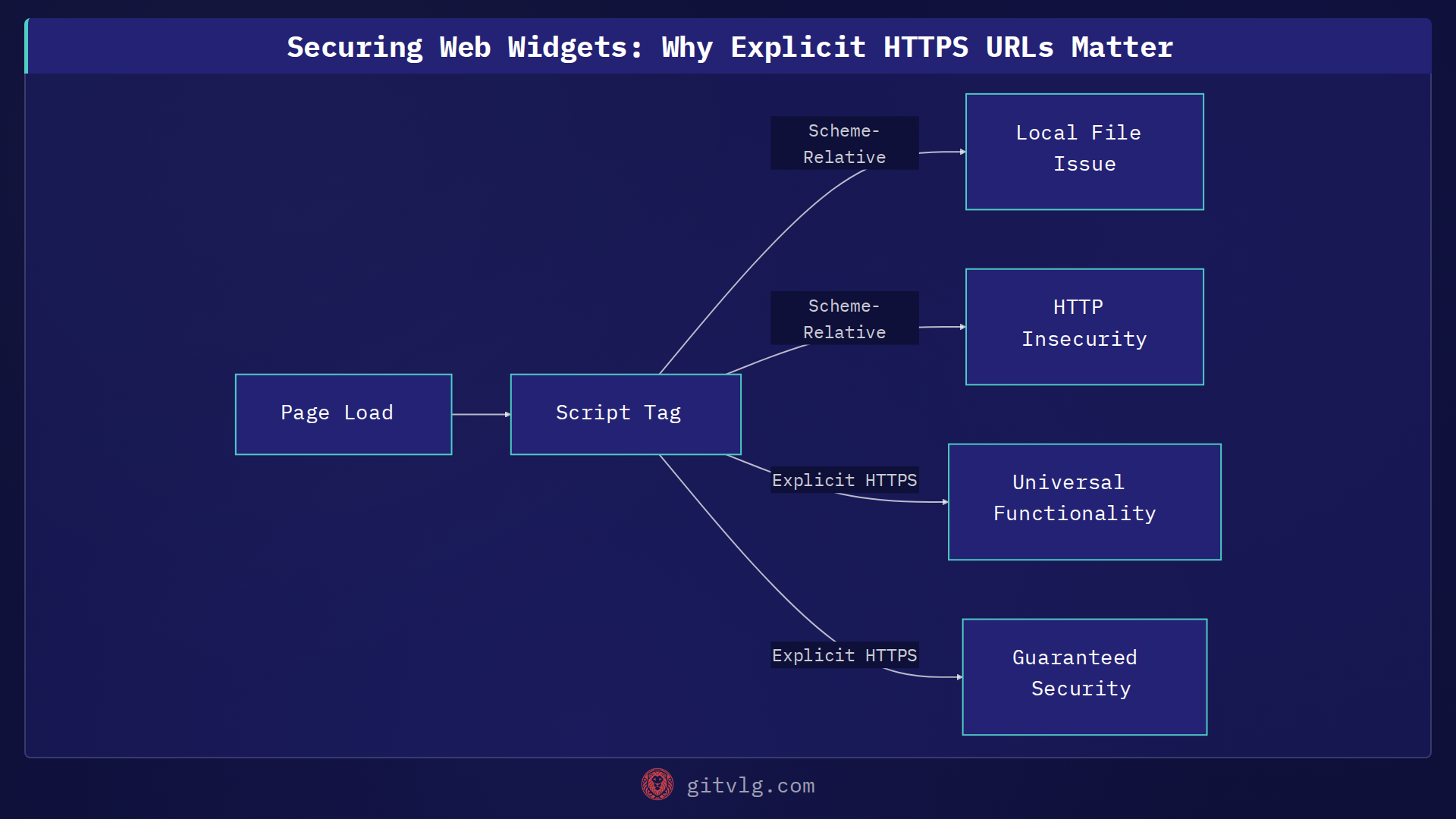
The Subtle Trap of Scheme-Relative URLs
During a recent code review for 'patitas-al-rescate', we identified a script tag for a translation widget that used a scheme-relative URL, like //translate.google.com/.... While this often works fine when served over HTTPS, it introduces vulnerabilities and functional issues in other contexts.
Specifically, when a page is opened directly as a local file (file:// protocol), the browser attempts to resolve file://translate.google.com/..., causing the widget to fail silently. Furthermore, if the main site is ever served without TLS (HTTP), the script will load insecurely over HTTP. This not only compromises security, potentially exposing users to man-in-the-middle attacks, but also triggers mixed content warnings in modern browsers, leading to a degraded user experience.
The Robust Solution: Explicit HTTPS
The fix is straightforward yet critical: always use explicit https:// URLs for external resources. By changing the script's src attribute from //translate.google.com/... to https://translate.google.com/..., we ensure several benefits:
- Universal Functionality: The widget will function correctly regardless of whether the page is accessed locally via
file://or served overhttp://orhttps://. This eliminates environment-specific bugs that are often tricky to debug. - Guaranteed Security: The script will always load over a secure, encrypted connection. This protects user data, prevents mixed content warnings, and builds user trust.
- Reduced Debugging: Eliminates an entire class of environment-specific bugs related to script loading, allowing developers to focus on feature development rather than chasing elusive widget failures.
The Takeaway
When embedding any external JavaScript, CSS, or other assets, resist the urge to use scheme-relative URLs. Prioritize security and reliability by always specifying the https:// protocol. This small change provides robust functionality and peace of mind across all possible deployment and access scenarios, making your web applications more resilient and secure.
Generated with Gitvlg.com